Stay Protected in Critical Situations
Every day we read about new kinds of cyberattacks, and keeping up with them is a constant challenge to protect your clients. What’s the best method for auditing critical business systems to ensure they are undisturbed? Adopting a cybersecurity framework is the answer. Not only are you able to accurately and effectively audit your client's environments, but it also enhances your reputation and adds response capabilities.
Select the Right Security Framework
There are several cybersecurity frameworks that MSPs and MSSPs can use. Here are a few to consider.

Address Every Stage of the Cyber Kill Chain
WatchGuard EPDR helps ensure that the Cyber Kill Chain is always interrupted, and attackers are turned away empty-handed. Discover how our cutting-edge technologies come into action specifically in a ransomware attack.
Simplify Security Framework Adoption

Prepare for MITRE ATT&CK with Behavioral Intelligence
Cybersecurity experts agree that behavior-based analysis is the latest security skill that will spot and remediate increasingly sophisticated threats. The MITRE ATT&CK Framework guides organizations to enhance their threat intelligence and assessment skills, and security providers and vendors alike are moving quickly to adopt it.
Visualize ThreatSync Intelligence in the WatchGuard Cloud Demo >

Apply NIST-CSF and NIST SP 800-171 for Comprehensive Alignment
NIST-CSF and NIST SP 800-171 are designed to foster risk and cybersecurity management communications amongst both internal and external organizational stakeholders. As a key security alignment reference document, companies can apply its Core, Implementation Tiers, and Profiles components to a wide range of security products and solutions.
WatchGuard Works Easily with Any Cybersecurity Framework

Stop the Cyber Kill Chain at the Start
Cyberattacks typically start with the theft of a user's credentials that give an attacker access to the network or a sensitive business account. WatchGuard AuthPoint provides the security you need to protect identities, assets, accounts, and information. Minimize the impact of lost and stolen passwords by making user access visible to your team.
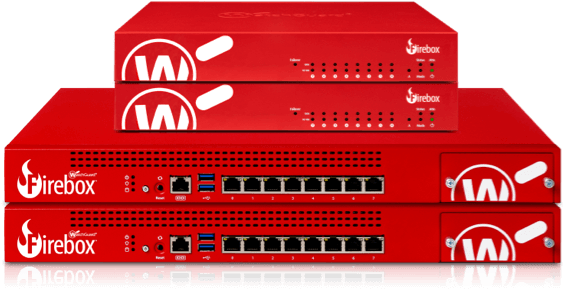
Every Framework Relies on a Firewall
IT security professionals count on firewalls to defend networks from a wide range of threats including advanced malware and ransomware. WatchGuard Total Security Suite offers even greater protection with security services and threat visibility tools available with any of our Firebox appliances, for layered security controls and broad, effective protection.

Security That Goes Everywhere You Go
Modern frameworks clearly call for security to extend past the corporate facilities and networks. WatchGuard EPDR protects laptops, computers, and servers with a broad range of endpoint protection (EPP) and endpoint detection and response (EDR) capabilities. It uniquely automates security actions for easy management and deployment.


42d6.jpg?itok=Q4nDG0qw)
e645.jpg?itok=1H1dwxJB)